Description
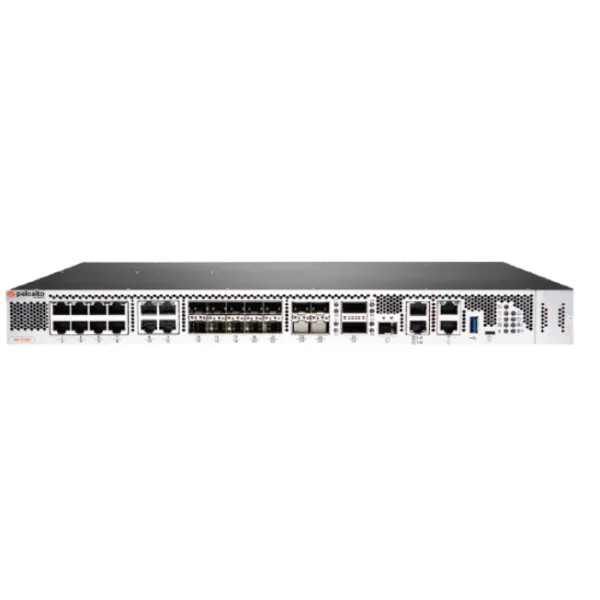
Palo Alto Networks PA-3430 Next-Generation Security Enterprise Firewall
In the rapidly evolving digital landscape, securing enterprise networks against sophisticated cyber threats is paramount. The Palo Alto Networks PA-3430 stands as a robust, high-performance firewall solution designed to meet the stringent security demands of medium to large-scale enterprises. Leveraging machine learning and advanced analytics, the PA-3430 offers unparalleled visibility, threat prevention, and streamlined management, ensuring your organization’s digital assets remain protected.
[ez-toc]
Key Features of Palo Alto Networks PA-3430
1. Machine Learning-Powered Threat Prevention
The PA-3430 integrates machine learning (ML) at its core, enabling:
- Inline prevention of file-based attacks and zero-delay responses to novel threats using cloud-based ML.
- Automated policy recommendations to reduce human error.
- Behavioral analysis of IoT devices for accurate classification and policy suggestions.
2. Advanced Threat Prevention Capabilities
Equipped with industry-leading security services:
- WildFire® identifies and prevents unknown malware.
- Advanced URL Filtering provides real-time protection against malicious URLs.
- DNS Security disrupts DNS-based threats.
- Integrated services block exploits, malware, and command-and-control (C2) attacks.
3. Unmatched Visibility and Control
- Full Layer 7 inspection of all traffic, regardless of protocol or encryption.
- Application-based policy decisions rather than port-based, enhancing security posture.
- Insights into all SaaS traffic, including unsanctioned applications.
4. Simplified Management
- Centralized administration through Panorama™ for visibility across distributed networks.
- Zero Touch Provisioning (ZTP) for easy deployment.
- Integrated SD-WAN functionality for seamless branch connectivity.
5. High Availability and Performance
- Active/active and active/passive HA modes ensure continuous protection.
- Predictable throughput with enabled security services.
Performance Specifications
| Metric | Specification |
|---|---|
| Firewall Throughput | Up to 25.5 Gbps |
| Threat Prevention Throughput | Up to 10.5 Gbps |
| IPsec VPN Throughput | Up to 12.2 Gbps |
| Max Concurrent Sessions | 2.5 million |
| New Sessions per Second | 240,000 |
| Virtual Systems (Base/Max) | 1 / 11 |
Networking Capabilities
- Interface Modes: L2, L3, tap, virtual wire (transparent mode).
- Routing Protocols: OSPFv2/v3 with graceful restart, BGP with graceful restart, RIP, static routing.
- Policy-Based Forwarding: Enables traffic steering based on defined policies.
- Multicast Support: PIM-SM, PIM-SSM, IGMP v1, v2, and v3.
- Bidirectional Forwarding Detection (BFD): Ensures rapid detection of path failures.
Encryption and VPN Support
- IPsec VPN: Supports AES-256 encryption, ensuring secure site-to-site and remote access connections.
- TLS/SSL Inspection: Including support for TLS 1.3, providing visibility into encrypted traffic.
Hardware Specifications
- I/O Interfaces:
- 12x 1G/2.5G/5G/10G Base-T ports.
- 10x 1G/10G SFP/SFP+ ports.
- 4x 25G SFP28 ports.
- 2x 40G/100G QSFP/QSFP28 ports.
- Management Interfaces:
- 1x 100/1000 out-of-band management port.
- 2x 100/1000 high availability ports.
- 1x 10G SFP+ high availability port.
- 1x RJ-45 console port.
- 1x Micro USB port.
- Storage Capacity: 480 GB SSD.
- Power Supply: Redundant 450-watt AC (average consumption: 155W; maximum: 190W).
- Dimensions: 1U, 19” standard rack (14.15” x 17.15” x 1.70”).
- Weight: 15.5 lbs (standalone device); 25 lbs (as shipped).
- Operating Environment:
- Temperature: 32°F to 122°F (0°C to 50°C).
- Humidity: 10% to 90%.
- Maximum altitude: 10,000 ft (3,048 m).
- Airflow: Front to back.
Security and Connectivity Features
App-ID Technology
- Application Recognition: Identifies applications regardless of port or protocol.
- Granular Control: Enables custom App-ID™ tags for precise policy enforcement.
- Legacy Rule Migration: Facilitates transition from Layer 4 to App-ID-based policies.
IoT Security
- Device Detection: Identifies unmanaged IoT devices.
- Zero Trust Implementation: Provides rapid protection through device classification and policy enforcement.
Encrypted Traffic Management
- Policy Application: Inspects and applies policies to encrypted traffic without decryption when necessary.
- Decryption Mirroring: Supports forensics and compliance requirements.
Multi-Factor Authentication (MFA)
- Network Layer Integration: Secures user credentials and application access through MFA.
AIOps Integration
- Predictive Analytics: Utilizes advanced telemetry and ML-powered analytics to anticipate and resolve potential disruptions.
Ideal Use Cases
The PA-3430 is tailored for:
- Medium to Large Enterprises: Seeking robust security solutions for complex network environments.
- Data Centers: Requiring high throughput and low latency.
- 5G Networks: Supporting mobile network infrastructure with 5G MEC, GTP, and SCTP security.
- Industries: Including healthcare, finance, retail, and government sectors that demand stringent security and compliance.
Why Choose Best Computer?
At Best Computer, we are committed to providing top-tier cybersecurity solutions. By choosing us, you benefit from:
- Authorized Palo Alto Networks Reseller: Ensuring genuine products with full warranty support.
- Competitive Pricing: Offering the best value for your investment.
- Expert Consultation: Assisting in selecting and deploying the right firewall solution for your needs.
- Comprehensive Support: Providing ongoing technical support and maintenance services.
Final Thoughts – Palo Alto Networks PA-3430 Firewall
The Palo Alto Networks PA-3430 Next-Generation Security Enterprise Firewall is a formidable solution for organizations aiming to fortify their network defenses against advanced cyber threats. With its ML-powered threat prevention, extensive visibility, and high-performance capabilities, the PA-3430 is an investment in your organization’s security and resilience.
For more information or to place an order, contact Best Computer Hub—your trusted partner in cybersecurity solutions.